2026 MSAB CTF: Android Questions
Where am I? (5 Points)
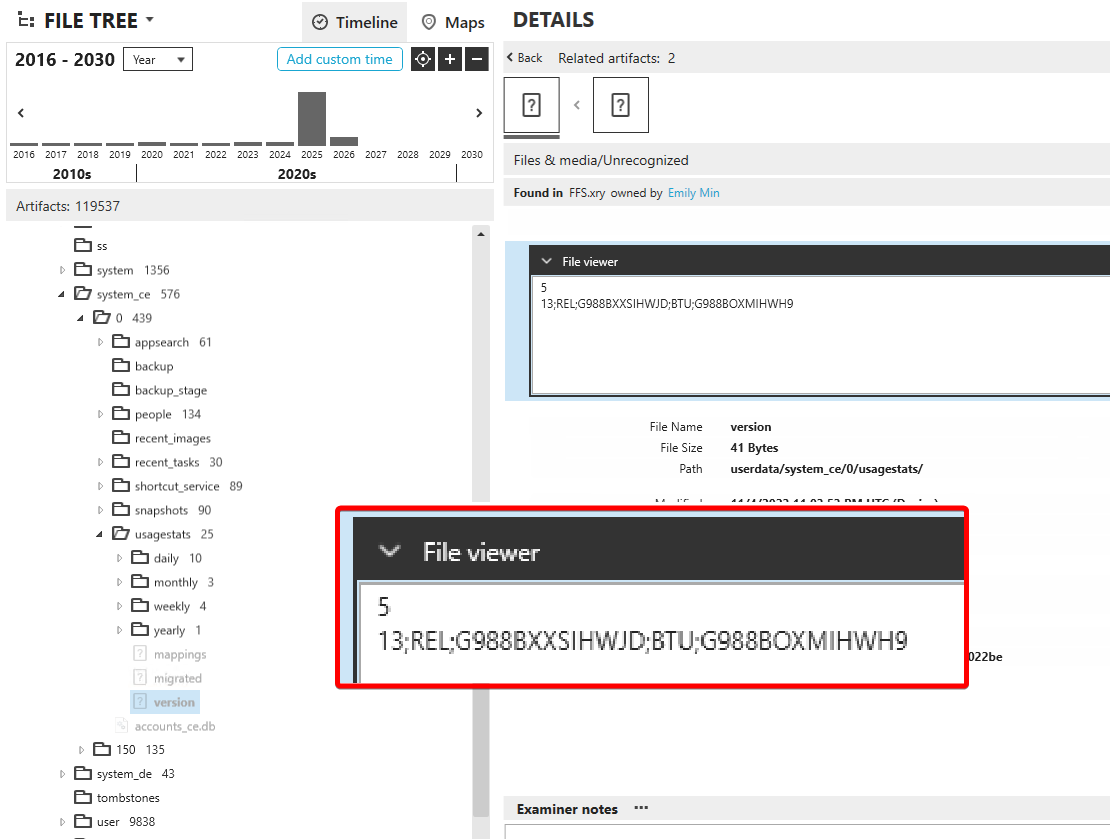
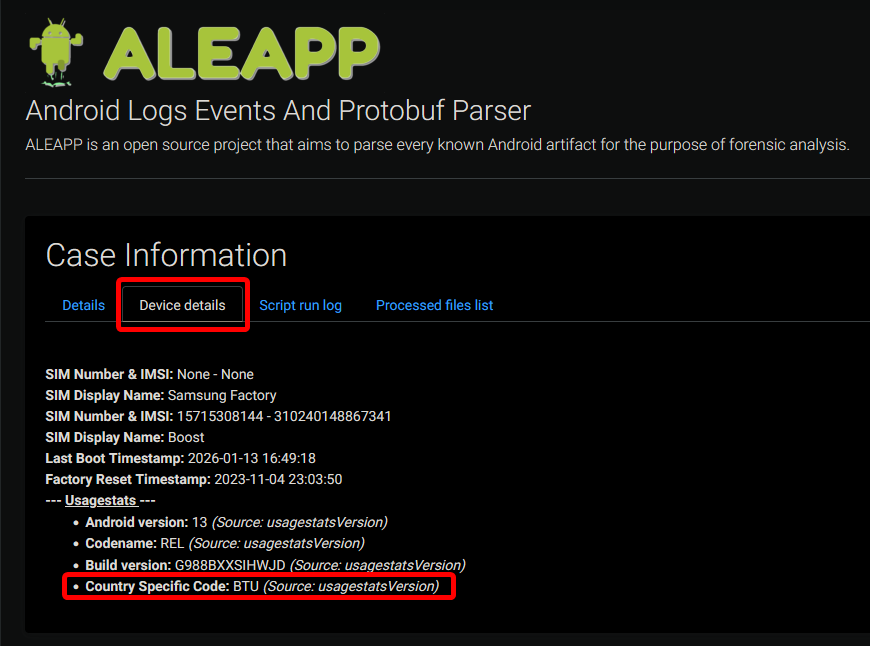
What is the CSC Country Specific Product Code associated with the device?
The CSC is located in /userdata/system_ce/0/usagestats/version. It is the three letter code.
It is also visible on the main page of the report in ALEAPP:
FLAG
BTU
Are you brave enough? (5 Points)
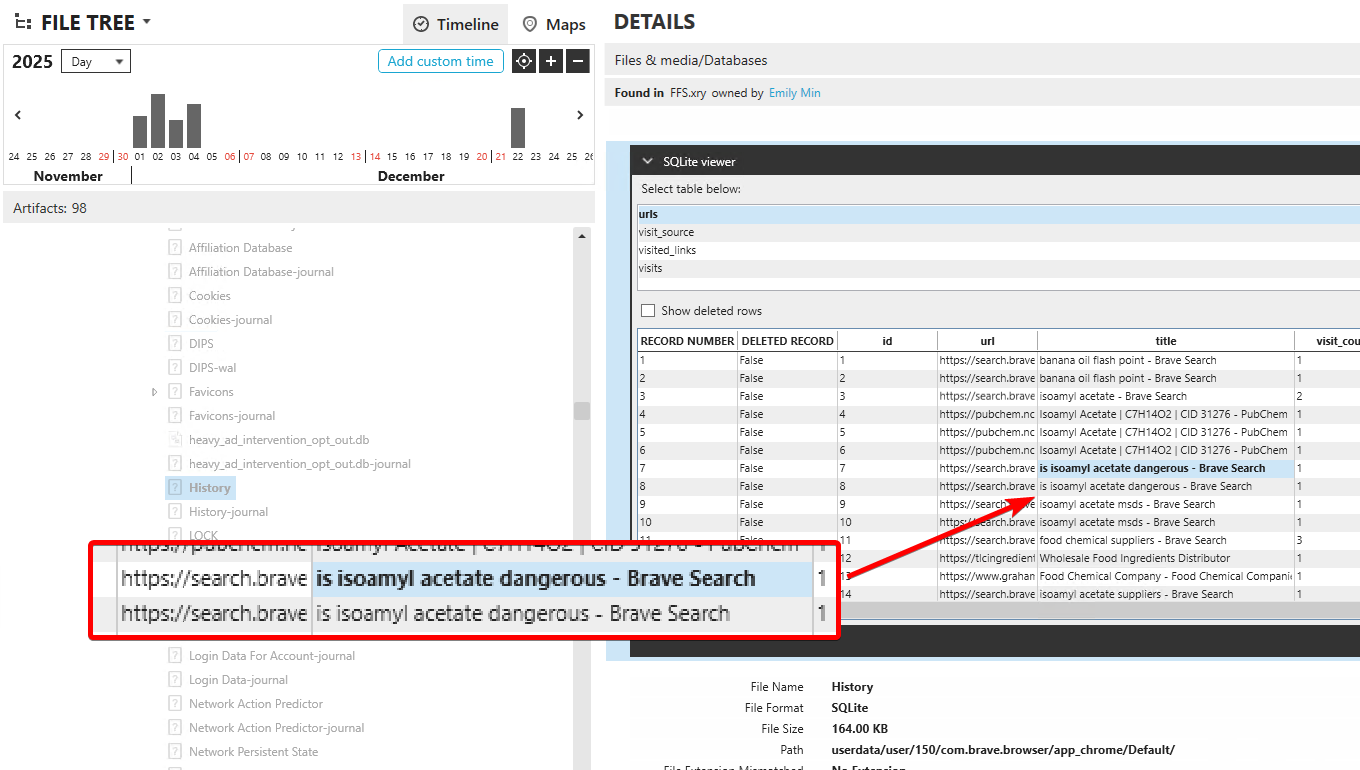
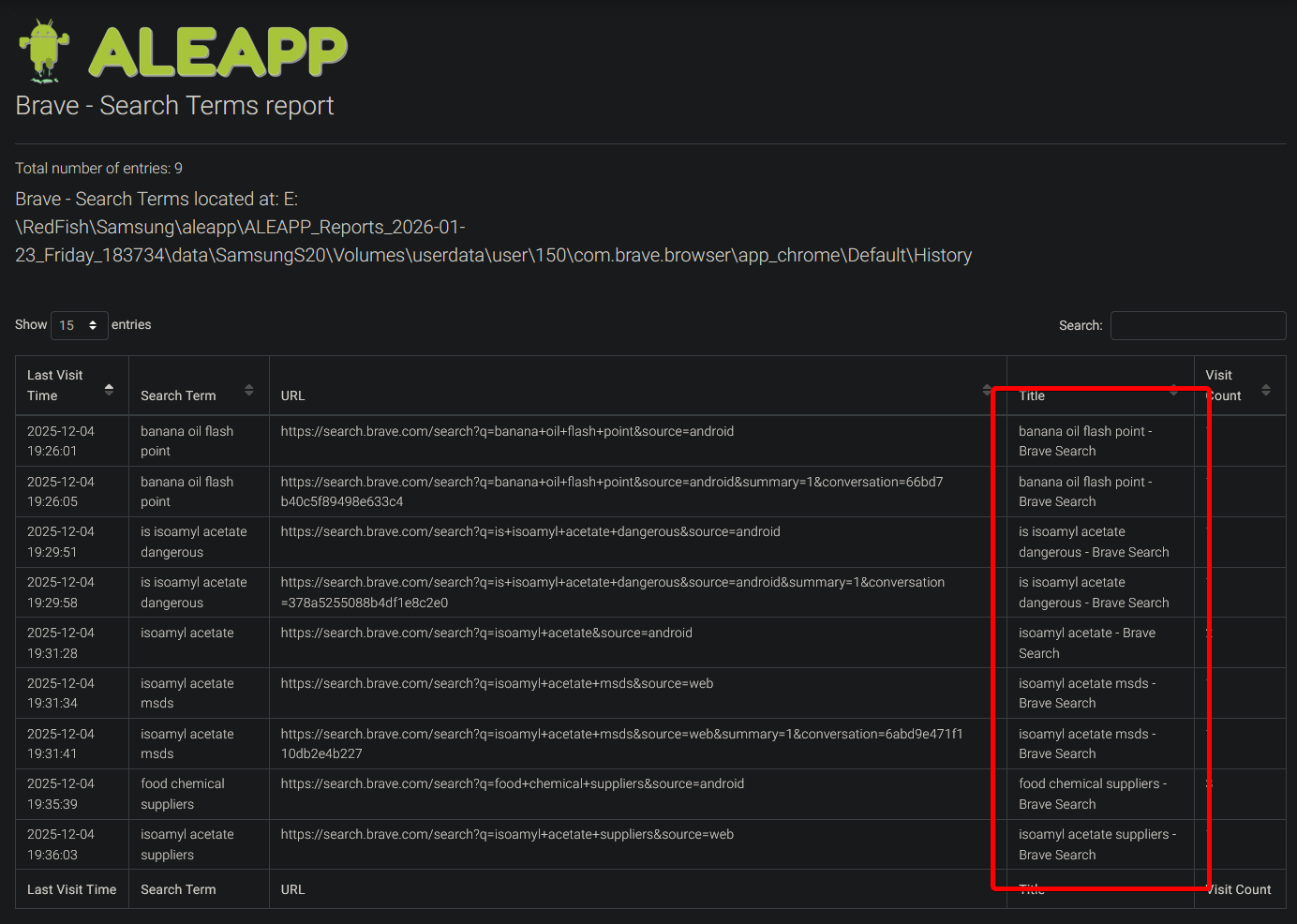
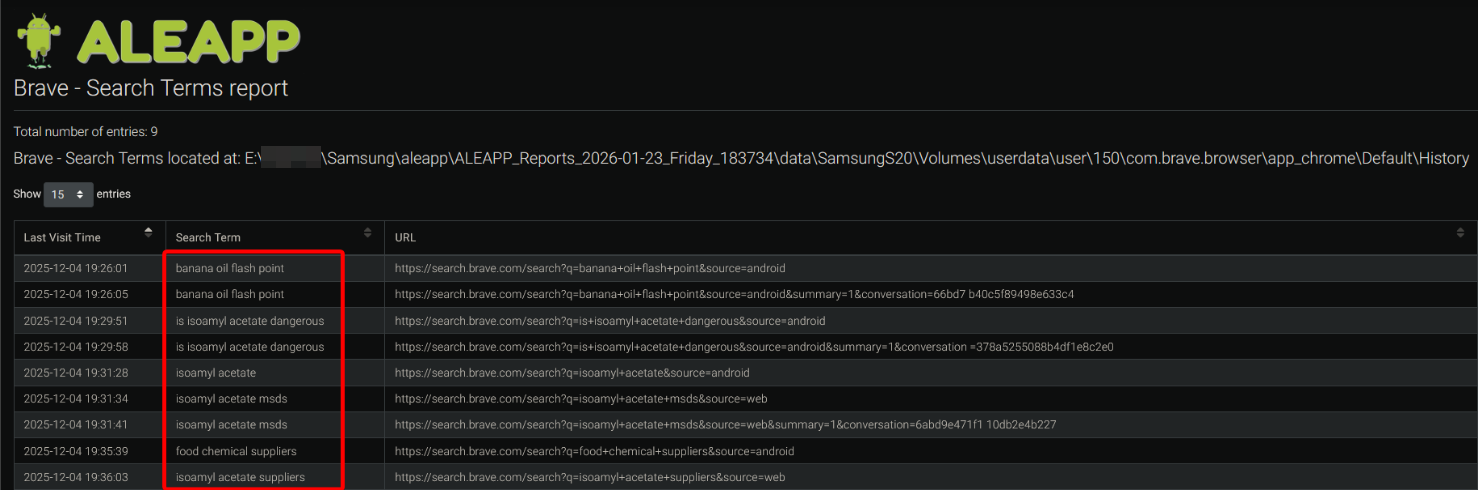
What "dangerous" substance was the user curious about?
The “dangerous” substance the user searched for was done through Brave, which was in the secure folder. (the app shows up in /userdata/user/150/ rather than /userdata/data/)
These searches are also visible in ALEAPP.
FLAG
isoamyl acetate
Antiques Road Show (5 Points)
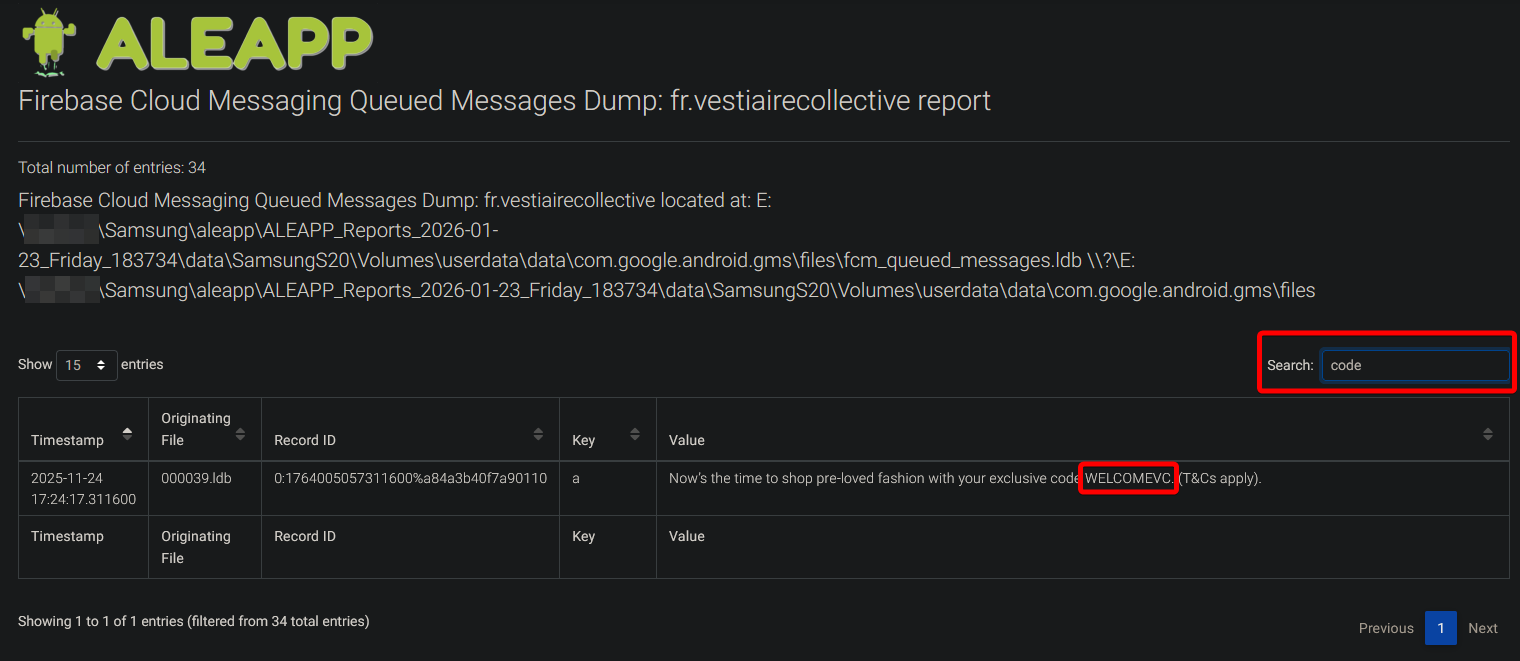
What code will help Emily save money on her antiques hobby?
Looking though the apps installed on Emily’s phone, there is one called “Vestiare Collective” which is for reselling pre-owned fashion (including antiques). In ALEAPP you can view the Firebase Cloud Messages for the app, and filter for “code”, where you will see the “WELCOMEVC” code is offered to the user through a notification.
FLAG
WELCOMEVC
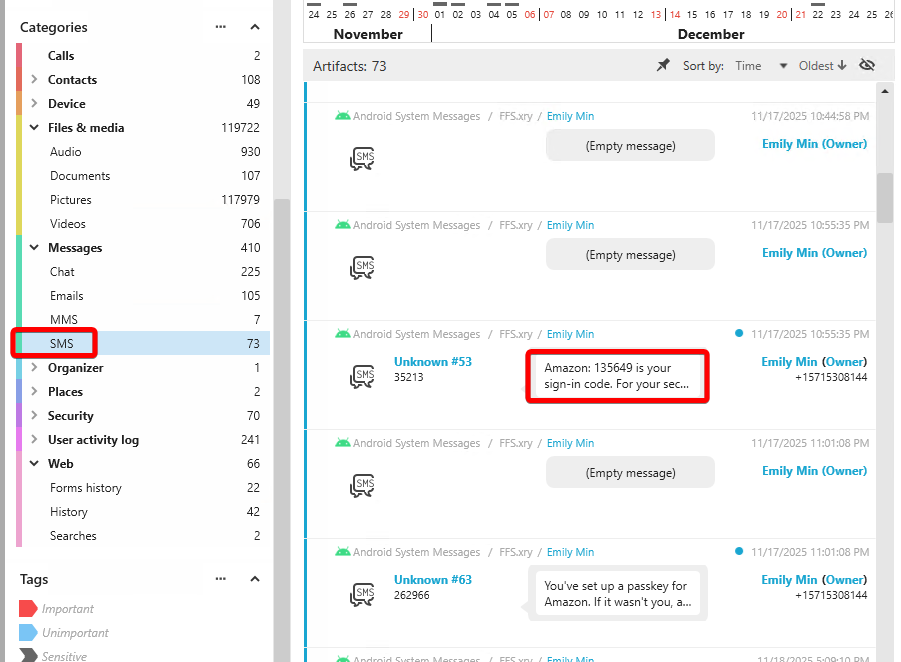
Special Delivery (5 Points)
What code appears in the first message from a Seattle-based company?
Look through the SMS messages category in XAMN, and sort by time. A quick google search against the first four companies to send codes to the user, Boost Mobile, Instagram, Microsoft, and Amazon shows that only Amazon is headquartered in the city of Seattle (Microsoft is Redmond-based, which is near but not in Seattle).
FLAG
135649
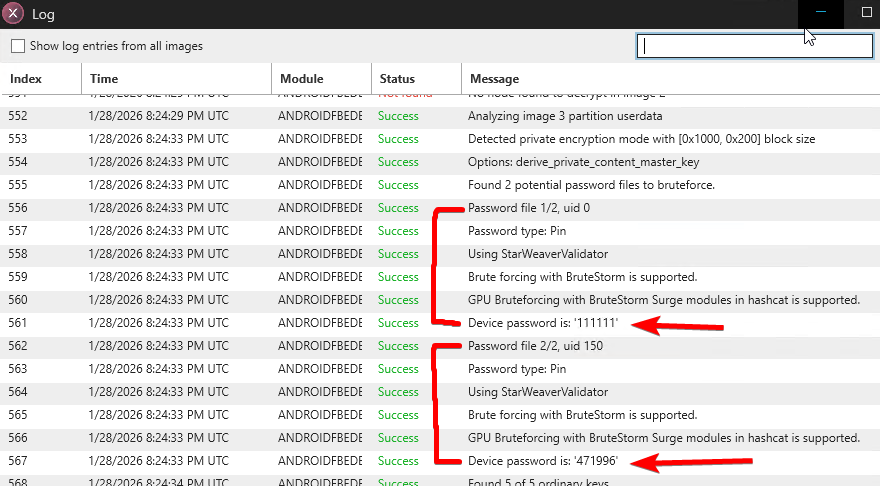
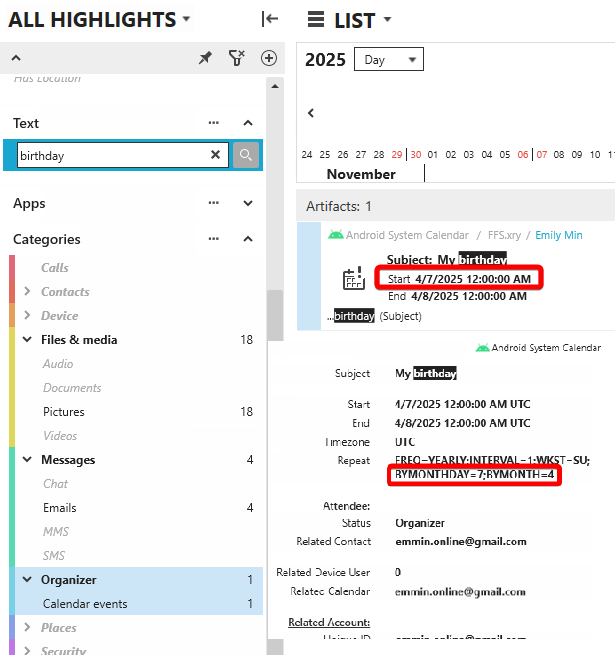
Flawless OPSEC (5 Points)
What personal information was used as the secure folder's unlock code?
XRY brute forces the code to the phone at acquisition time, you can see this info in the extraction log:
We have the default user’s (0) pin as ‘111111’ and user 150 (which is the secure folder) as ‘471996’. This looks like a date, and we get a pretty good hint that this is the user’s birthday if you search the calendar for “birthday”.
Throughout the phone there are many accounts that have “96” appended to the username, which is common with birthdays.
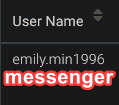
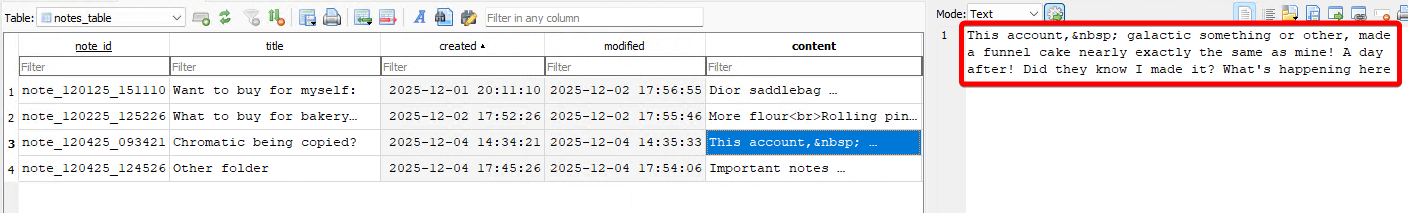
At this point you can probably guess the answer is the user’s birthday, but the real smoking gun is inside the notes application’s database, at /userdata/data/com.notes.todolist.notebook.checklist.notepad.android/databases/notes_db:
This is a ROT13 cipher, when decoded it results in “password is my 6 digit birthday”
FLAG
Birthday OR Emily’s Birthday
Fake of Bake (10 Points)
What AI should be credited for making a picture of a cupcake?
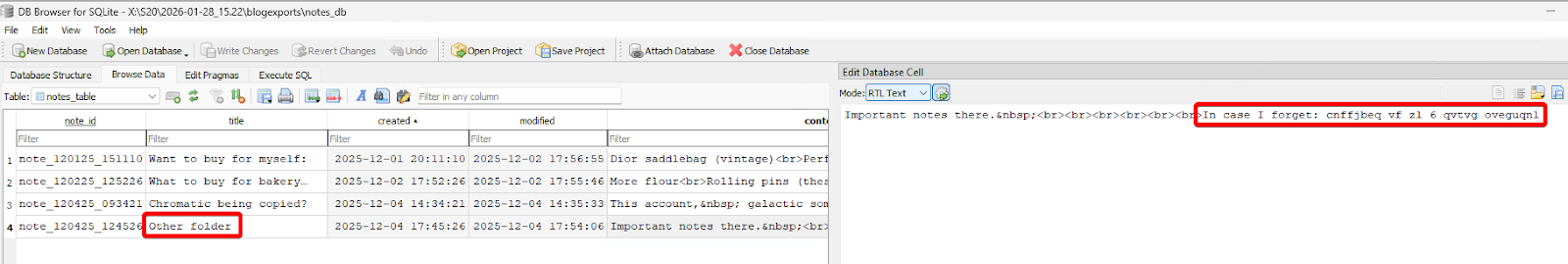
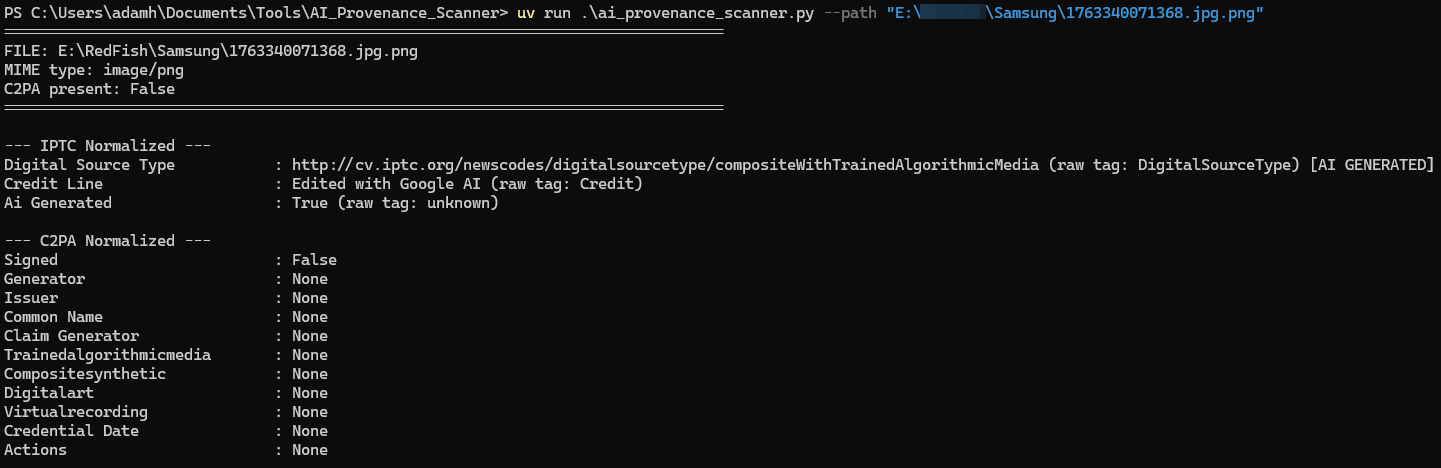
Find the image of the cupcake inside the user’s pictures folder at /userdata/media/0/Pictures/1763340071368.jpg (it’s actually a PNG), and extract it.
Alexis Brignoni’s AI Provenance Scanner tool is really useful here, where you can pass the image along to the tool and it will determine that it was edited with “Google AI”, which is also known as Gemini.
FLAG
Google AI OR Gemini
Honey I'm Home (10 Points)
What house number was copied?
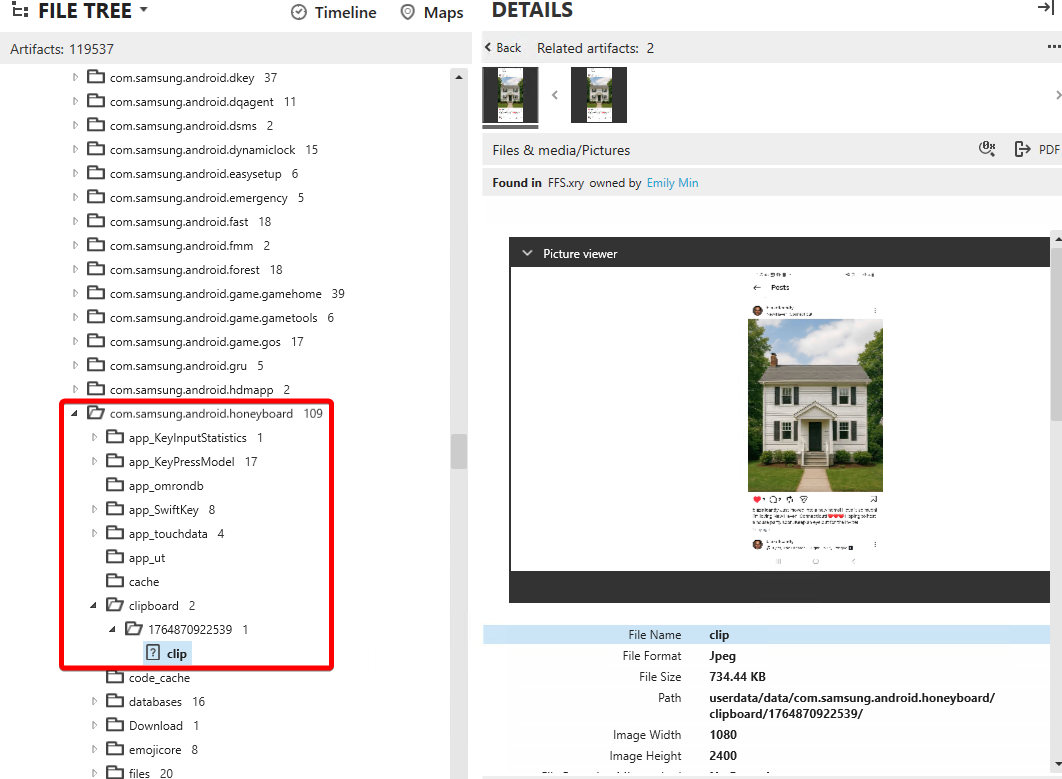
Look inside the honeyboard’s clipboard storage folder located at /userdata/data/com.samsung.android.honeyboard/clipboard/.
There is a subfolder with a timestamp as its name, with a file inside with no extension, called “clip”
Open the image in the pop-out view, and zoom in. You will find the house number.
FLAG
985
Focus on Me (10 Points)
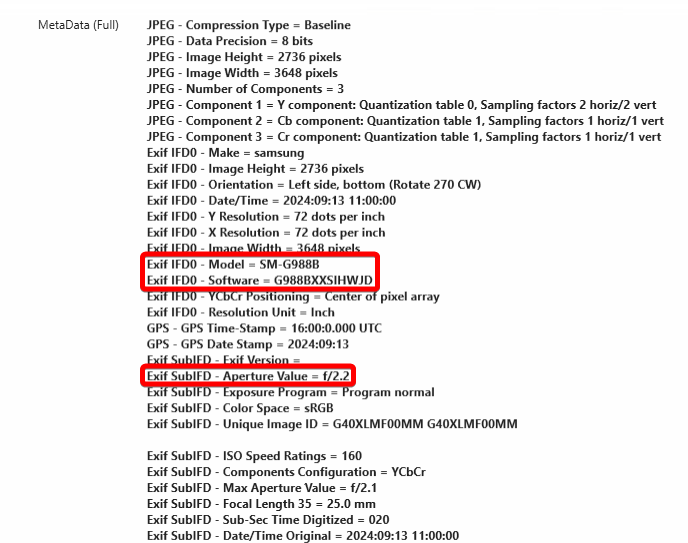
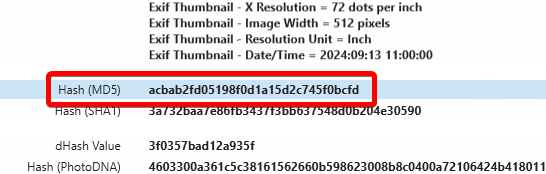
What is the MD5 hash of the original photo of Emily taken with a f/2.2 aperture?
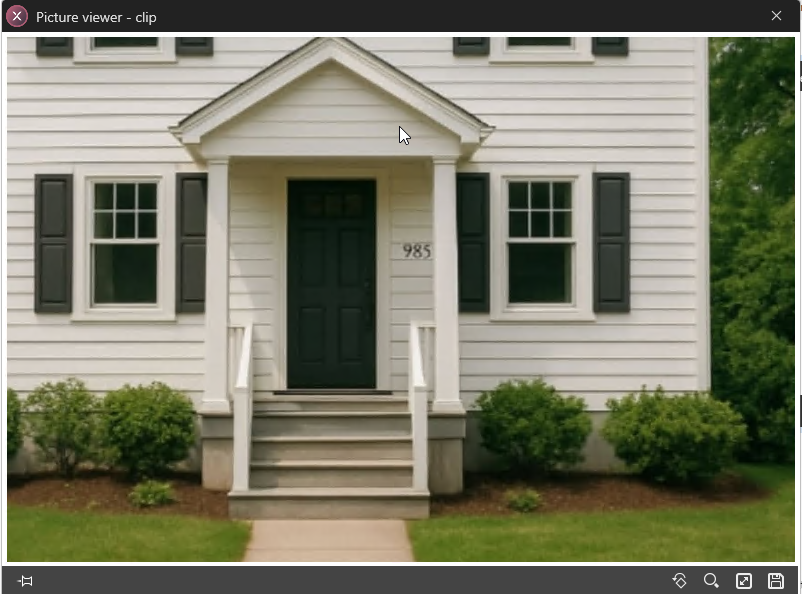
There are a couple places where there are pictures of Emily, but an original photo taken on the phone would be inside the [user id]/DCIM/Camera/ directory. If we find other copies, the hash may be different as lots of data tends to get removed when the phone saves copies in other places and the resolution changes, so it’s crucial to find the original one. Inside this directory on the phone, there are two images. One has a picture of Emily and one is a logo for Chromatic Confections.
Scroll down to see the metadata for this image. We can confirm that the picture was taken on this same model of phone, and the aperture matches the one in the question.
Scroll down a little further and you will find that XAMN has already stored the hashes for this image.
FLAG
acbab2fd05198f0d1a15d2c745f0bcfd
Comin straight from the underground (25 Points)
Which city is correlated with the musical reference in Emily's secret instagram account?
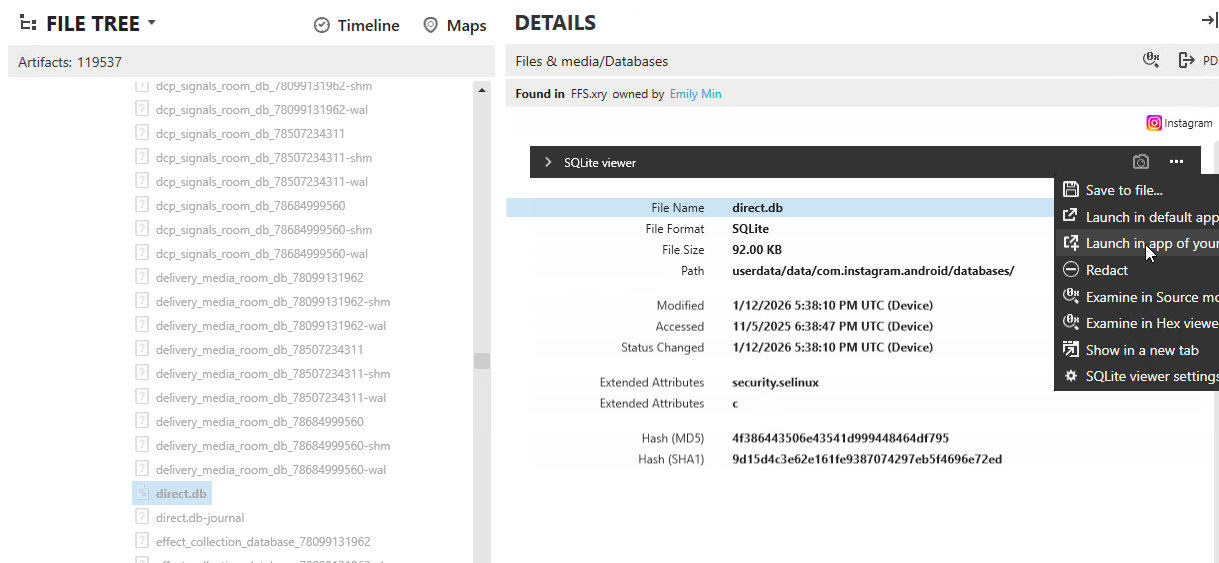
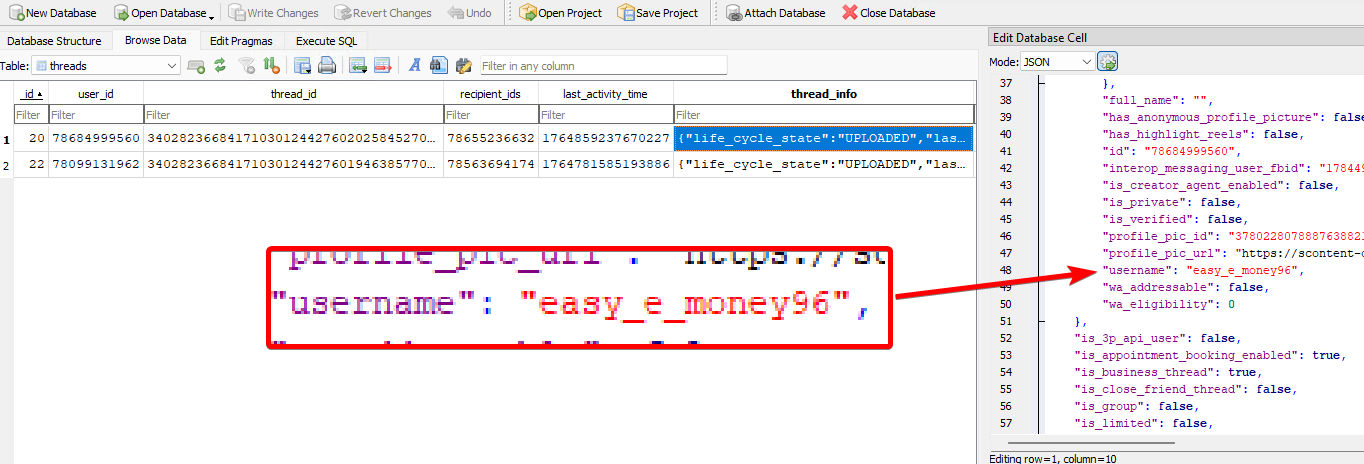
Find the Instagram app’s direct.db at /userdata/data/com.instagram.android/databases/direct.db to locate the DM for each account:
Open in DB Browser to see the blob information, and head to the threads table where you can see information about each conversation.
The username for her alternate account is easy_e_money96
This is a reference to Eazy-E, who helped make the song Straight Outta Compton as part of N.W.A.
image source: wikipedia
FLAG
Compton OR Compton, CA
Bilingual (not really) (25 Points)
Other than the en-US, what locale was configured?
This can be found in a few locations:
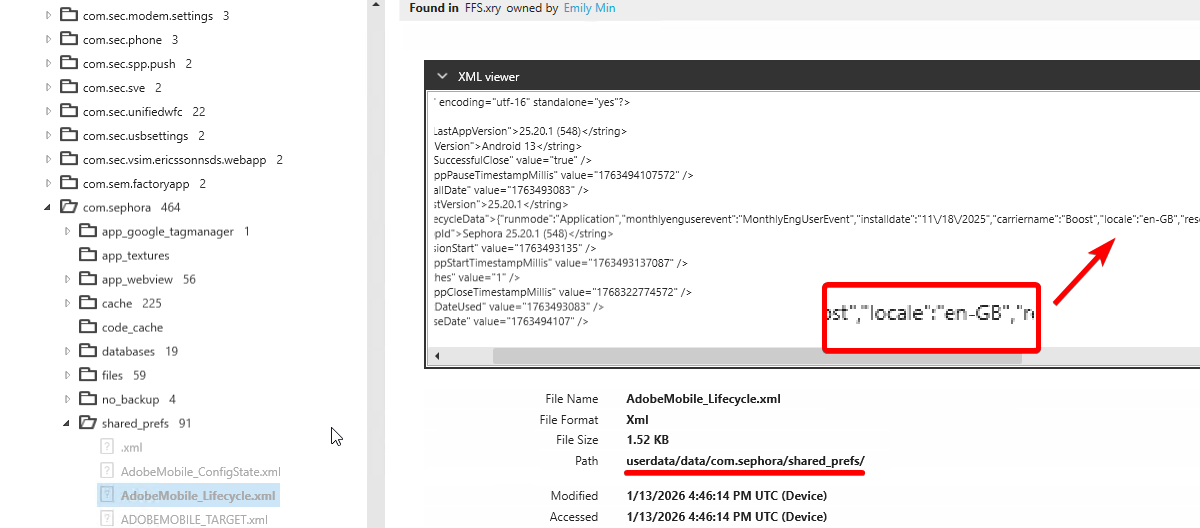
In the apps themselves, most commonly in an XML file in their shared_prefs folder:
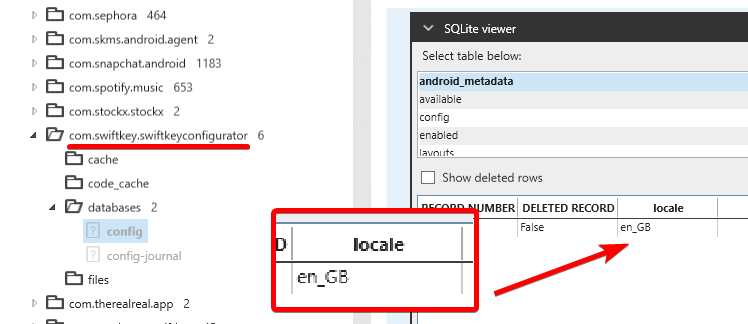
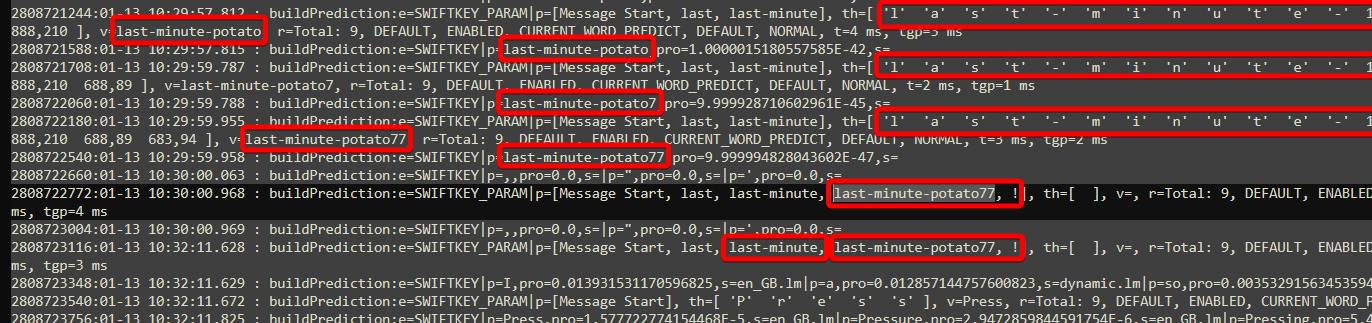
The SwiftKey app has the locale in its database
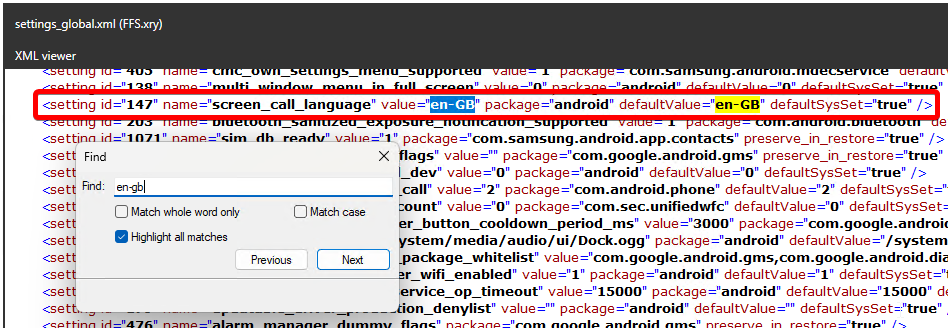
The settings_global.xml file at /userdata/system/users/0/settings_global.xml also has the other locale.
FLAG
en-GB
Let me IN! (25 Points)
What was the account login password for the user's password manager?
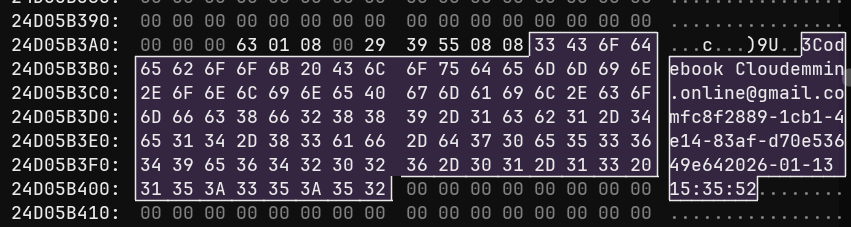
This is a RAM question. Looking through the installed apps, the only password manager is Codebook, with the package ID of net.zetetic.strip.
If you search for the product, you can find that there is a Codebook Cloud account for the emmin.online@gmail.com account, with a user ID of fc8f2889-1cb1-4e14-83af-d70e53649e64.
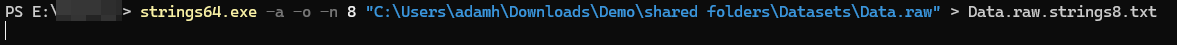
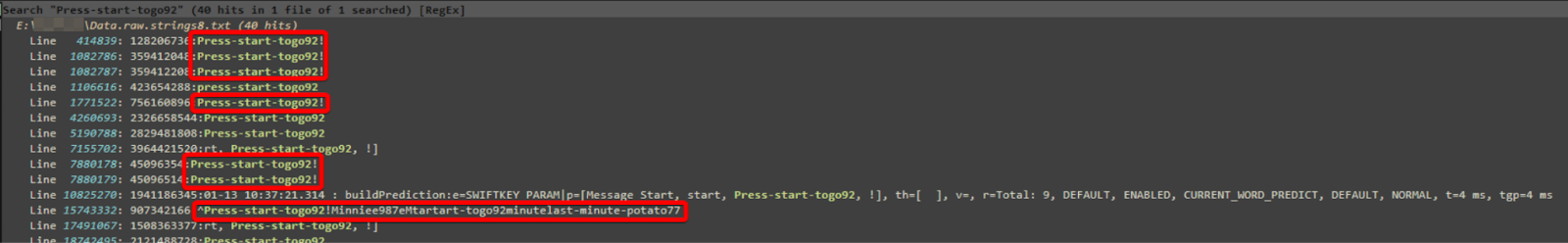
From here, I would recommend making a strings file, I used the strings64 utility from Sysinternals:
I used regex from here to find the password, luckily this was intact inside a JSON object:
FLAG
last-minute-potato77!
Keys to the city (25 Points)
What is the master password for the user's password manager?
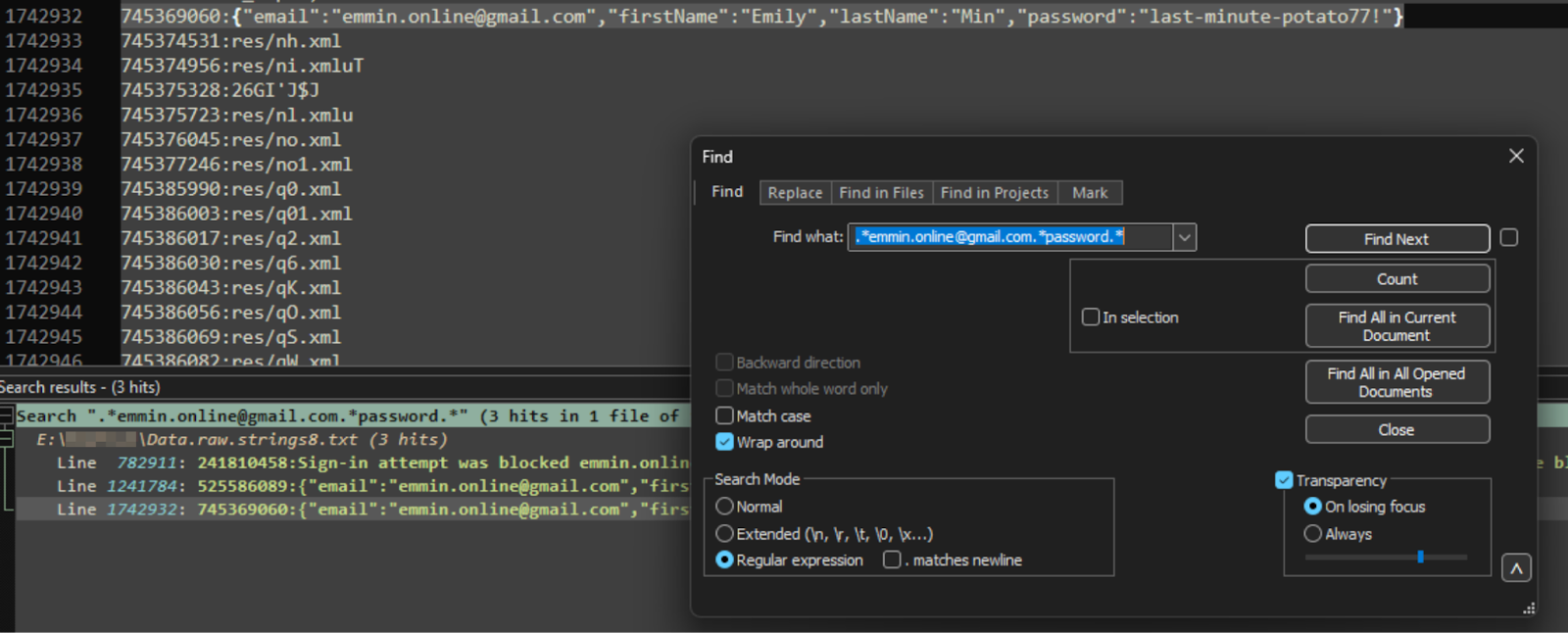
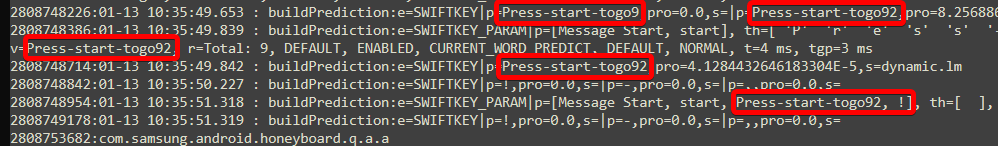
This is much easier to solve if you have finished the last question. If we search for this password string, there are a lot of hits that start with “buildPrediction:e=SWIFTKEY”. This is actually the RAM data from the com.samsung.android.honeyboard app. Fortunately, it has timestamps that mark the time the user typed the characters:
Just scroll a little further down, and you can see the user typing another password right after, this is the master password for the password manager that the user has to type after logging in. There is an exclamation mark after the string, and it doesn’t get combined with the rest of the text in the honeyboard application.
If we search it without the exclamation mark, we can find it alongside it in other locations.
FLAG
Press-start-togo92!
That's chilly! (25 Points)
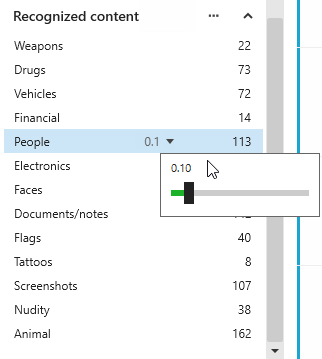
What property of a key chemical did the user search for in private browsing/incognito?
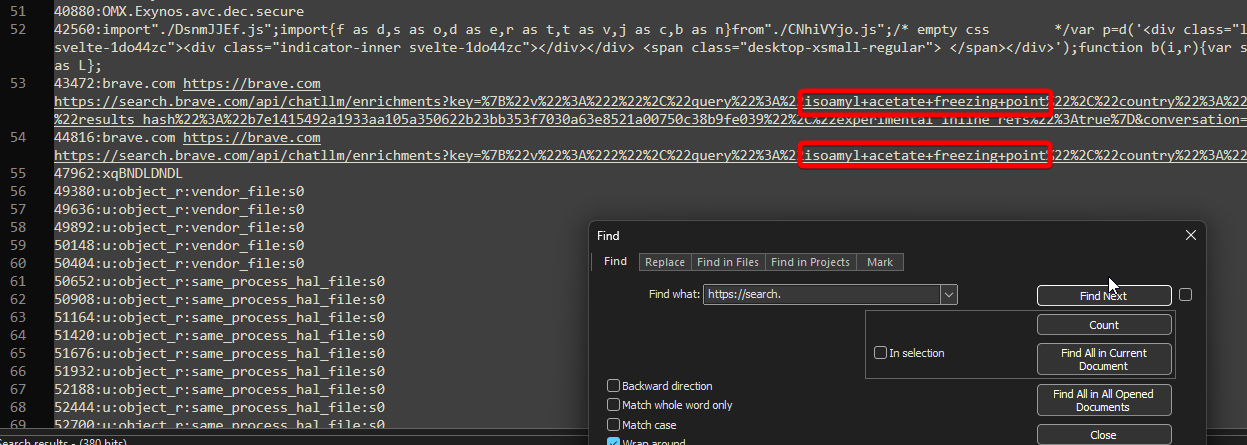
In the FFS image, you can find that the user looks up the flash point of Isoamyl Acetate, but in private browsing this would not show up in a typical FFS image.
Looking for these properties that didn’t show up in XAMN or ALEAPP, you can search for “https://search.” to find all searches (Google, Brave, Yahoo, and many other search engines all use search.[website].com format):
FLAG
freezing point
Flash Dance (50 Points)
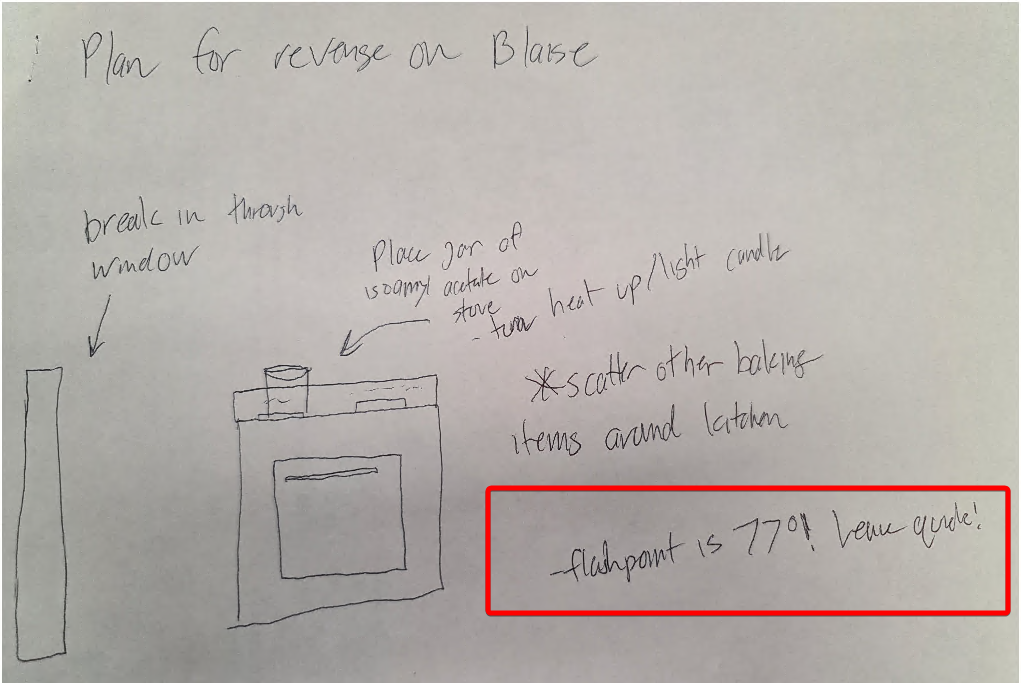
What is the important temperature in Emily's SECRET plan? (degrees Fahrenheit)
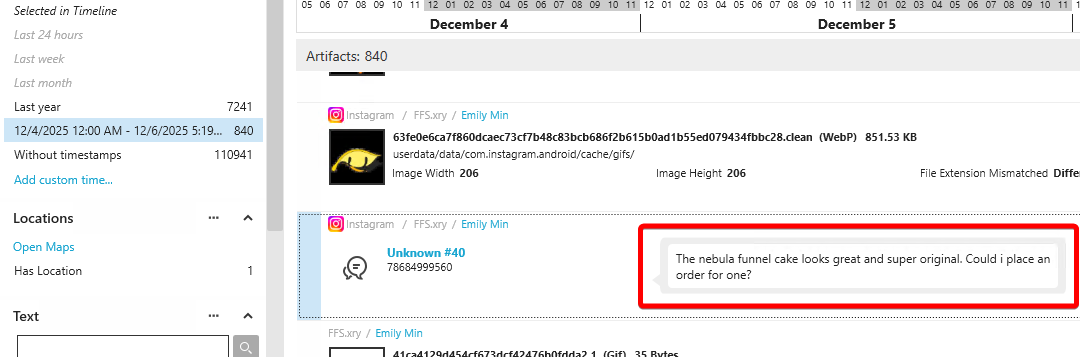
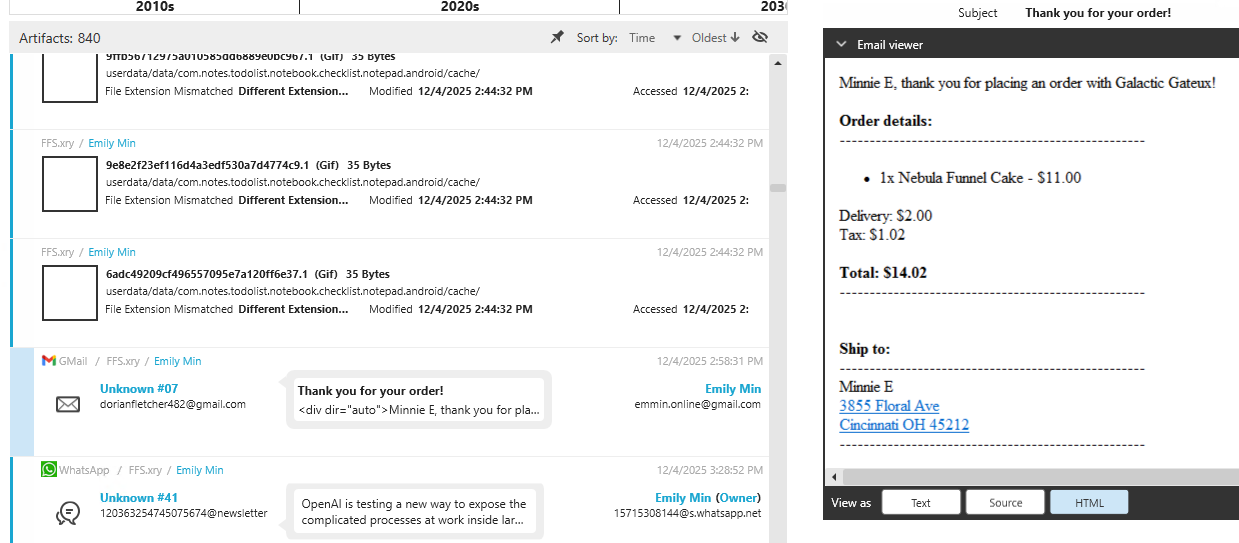
It’s useful to get a timeline of events here. Emily sends a message from her easy_e_money account to galactic.gateaux talking about a Nebula Funnel cake and how it looks “great” and “super original”.
Just before, there is some activity in a 3rd-party notes app. Looking at the database for that app (com.notes.todoist.notebook.checklist.notepad.android), at /userdata/data/com.notes.todolist.notebook.checklist.notepad.android/databases/notes_db, we can see a note saying that the “galactic” account made a funnel cake nearly exactly the same as hers (rainbow funnel cake) just one day after. Afterwards, there is a note about important information being in the “Other folder”
This is a reference to the secure folder. But before that happens, she orders one of the cakes for herself.
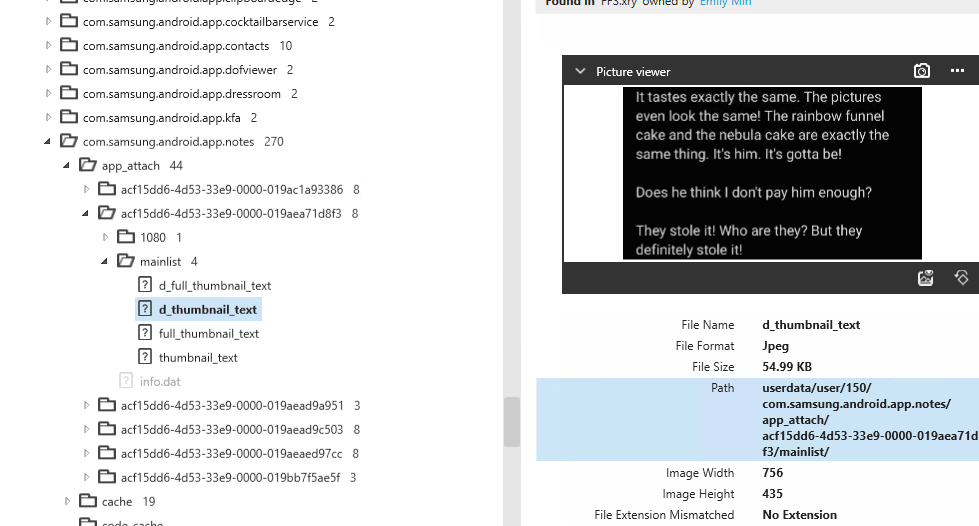
Then, once she tries it, she notes her reaction in the secure folder’s notes app.
Afterwards, she makes searches about Banana oil, and later Isoamyl Acetate (commonly used artificial banana flavoring) in Brave inside the secure folder.
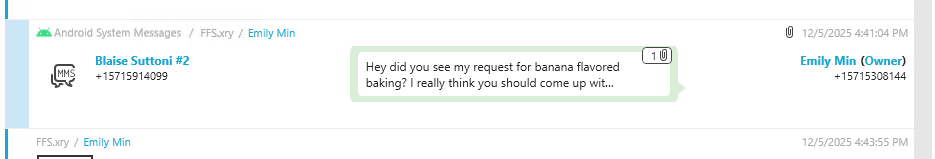
She makes a plan for revenge, a photo inside the secure folder can be found at: /userdata/media/150/DCIM/Camera/20251205_104002.jpg. She writes her plan down, and a critical temperature can be found, the flash point.
The day after, she requests Blaise to make banana flavored baked goods, and to practice making them, presumably so that he would reasonably have a bunch of banana flavoring in his house already.
FLAG
77
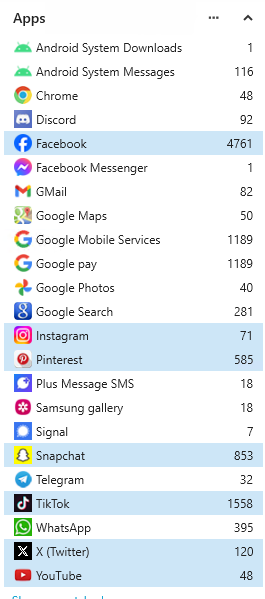
A high hurdle (50 Points)
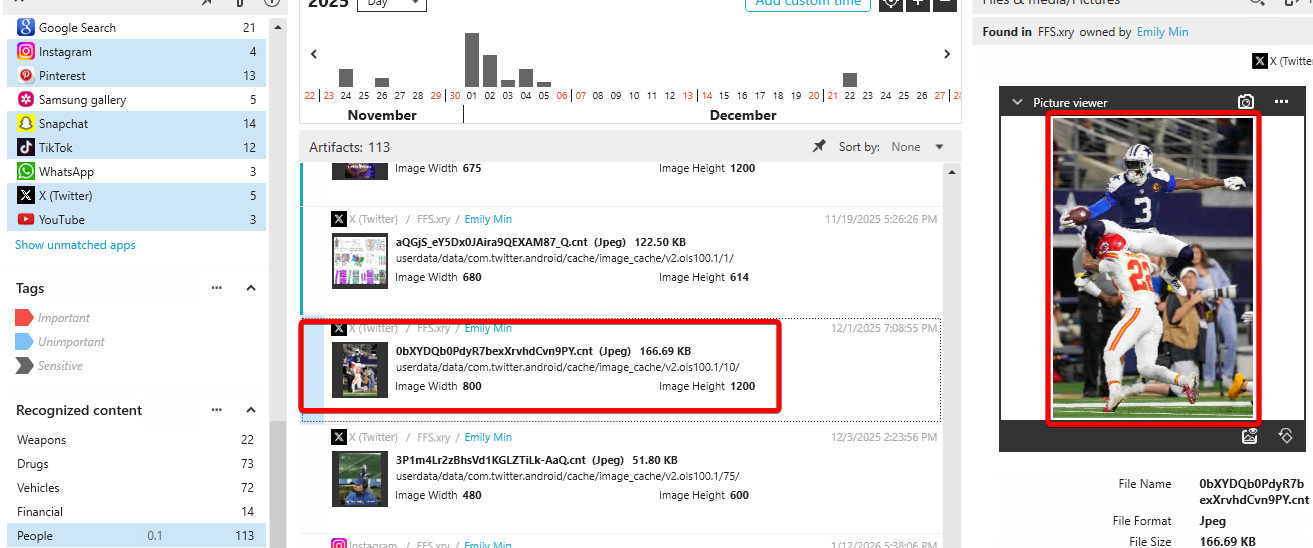
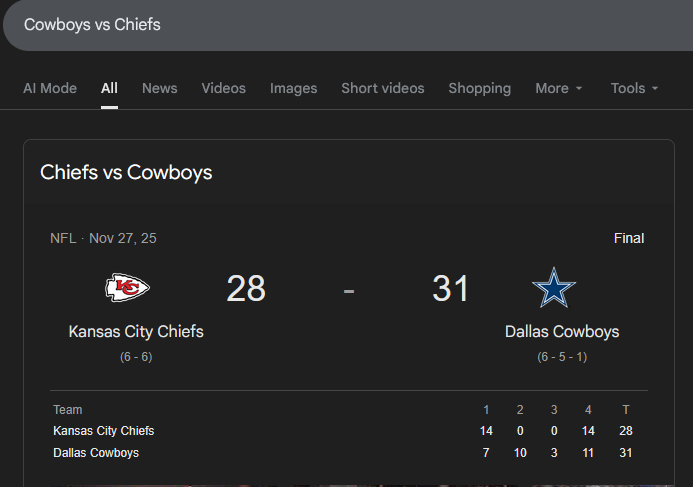
A wide receiver was viewed on a social media app jumping; when was the original photo taken? (Format: YYYY-MM-DD)
You’ll have to look through the social media apps to make a shortlist, and filter to only see pictures:
It also helps to use XAMN’s recognized content features to sort for images containing people:
Note: There are many false positives here as XAMN tries to capture everything.
Eventually, you can find a cached picture of a football player jumping. You can reverse image search to find who this is (George Pickens), confirm his position (wide receiver), and find the date of the game (Cowboys vs Chiefs, Thanksgiving Day).
FLAG
2025-11-27
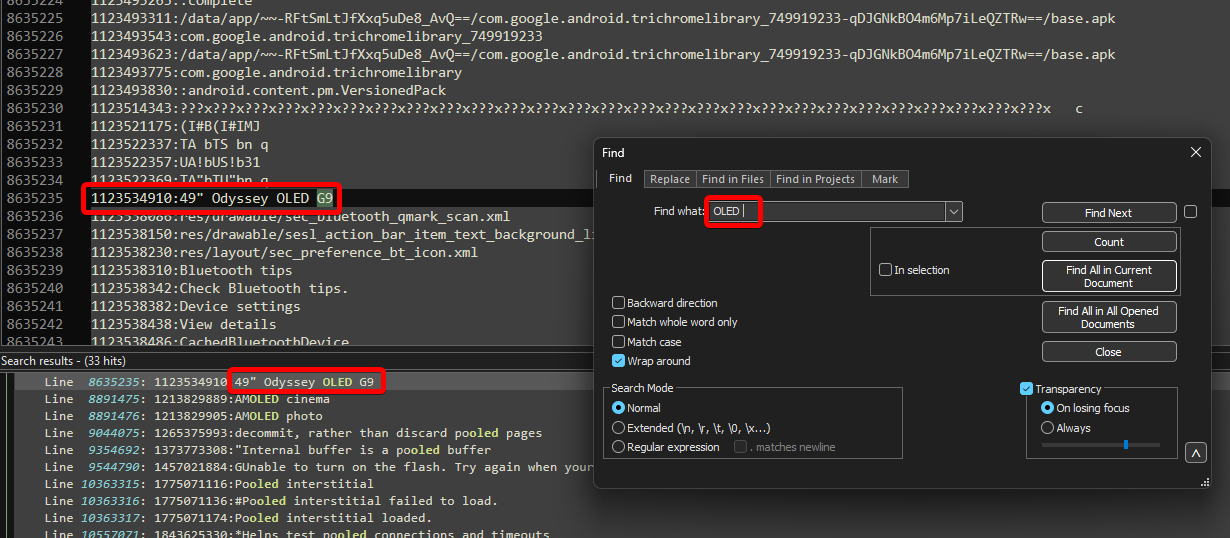
Fancy-pants monitor (50 Points)
What size is the display that was near the device? (diagonal, inches)
Create a wordlist of technologies that might be found in fancier monitors. Then, search the dump for each of these words until you come across a monitor.
If you search for the string “OLED ” (with the space) you should come across it pretty quickly. The reason this shows up in RAM is because it renders for the user when inside the Android settings app, when scanning for advertising Bluetooth devices.
FLAG
49”
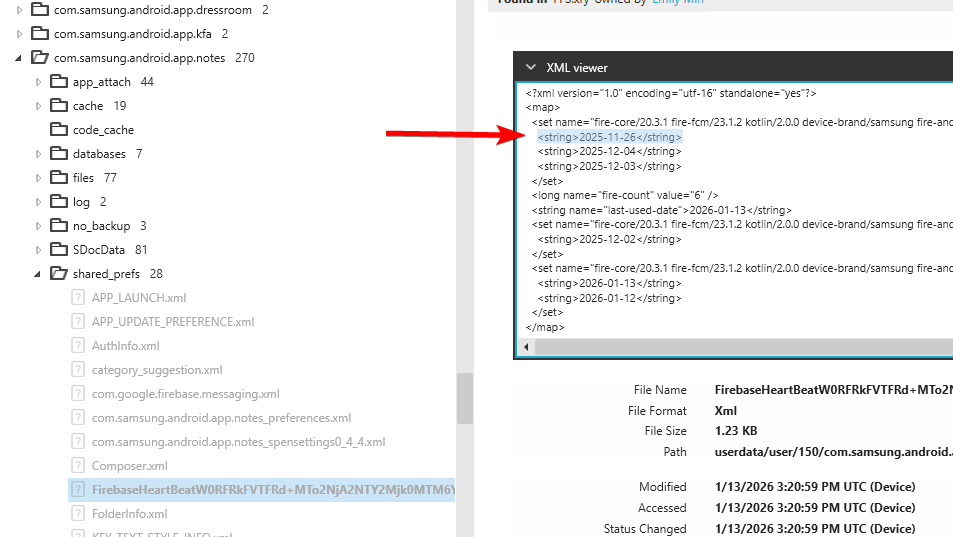
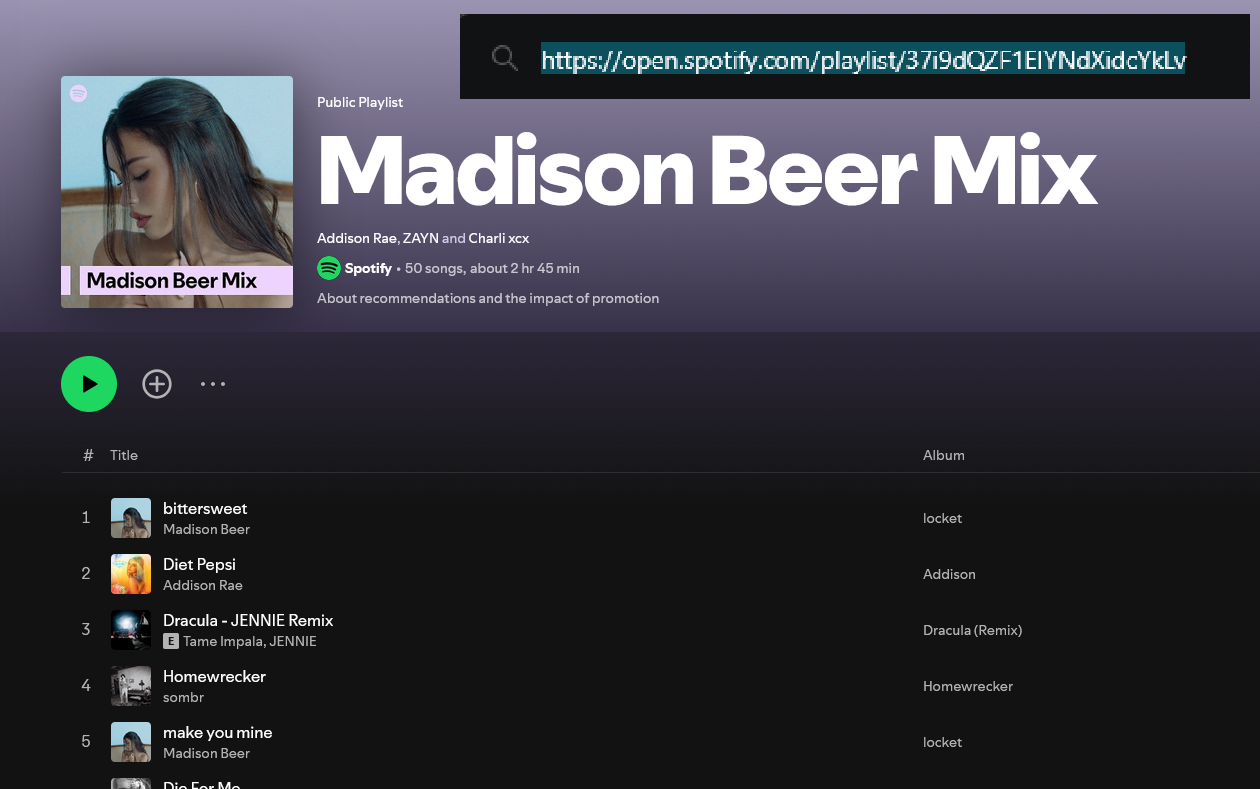
Spot if I can answer (75 Points)
What is the title of the playlist that the user was listening to on the day they first used their hidden notetaking app?
Hidden notetaking app refers to the Samsung Notes app in the secure folder. You can find the day it was first opened by checking the FirebaseHeartBeat….xml file, and finding the earliest date:
/userdata/user/150/com.samsung.android.app.notes/shared_prefs/FirebaseHeartBeatW0RFRkFVTFRd+MTo2NjA2NTY2Mjk0MTM6YW5kcm9pZDplZjllYmIzMmExNGI4NmZm.xml
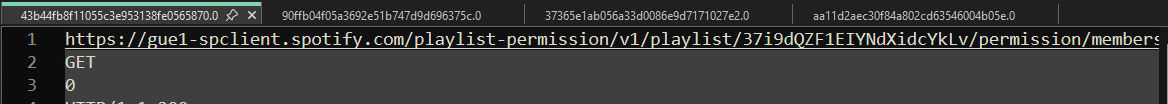
Focusing on events that happened on 2025-11-26, search Spotify’s http cache, located at:
/userdata/data/com.spotify.music/cache/http-cache/
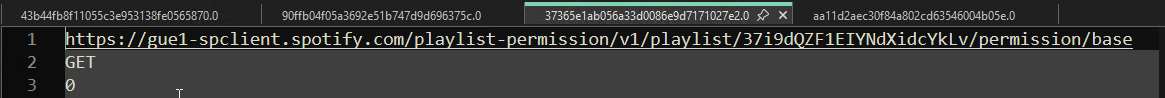
In here, you will find multiple files with that date as the modified date, showing the user browsed to this specific playlist:
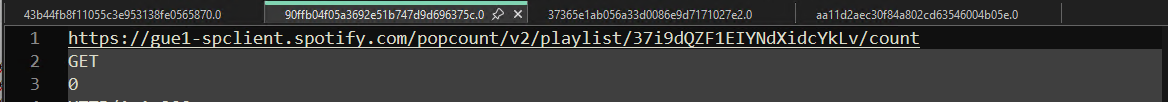
Immediately after this file, playback starts:
You can see the title of the playlist by copying the ID into a Spotify URL.
FLAG
Madison Beer Mix
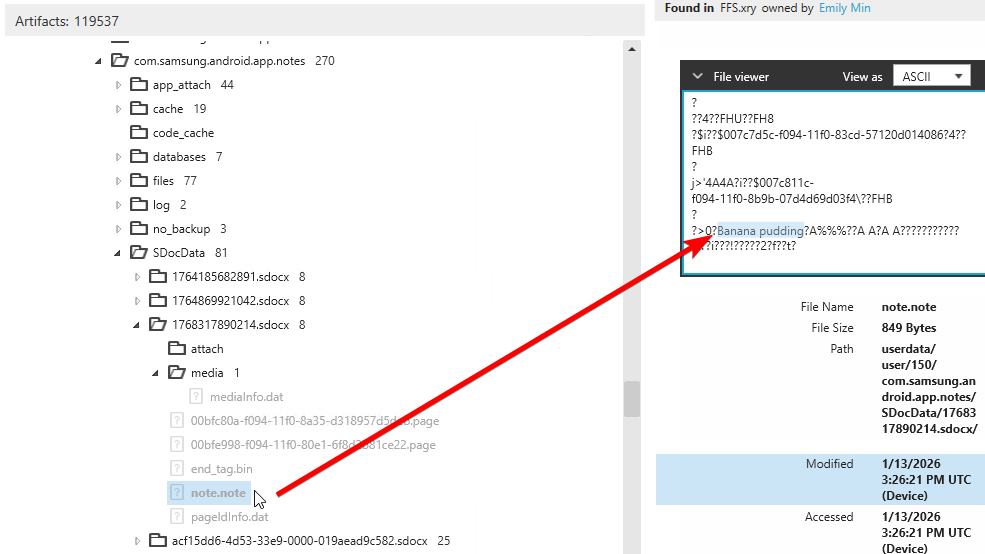
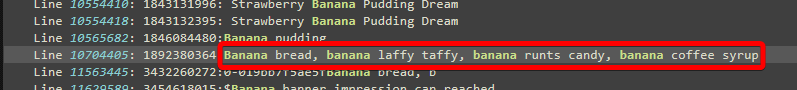
Scratch that (75 Points)
What list of banana themed product ideas did the user jot down, then replace?
In the FFS image we can see that the user has a note with the text “Banana pudding” inside the Samsung Notes app in the secure folder.
But the question asks specifically for what was deleted from here. If we look for “Banana ” (with the space), we can find references to both this Banana pudding and a list of other goods that aren’t found in the FFS image. Without context of what data belongs to what app, this can be pretty tricky.
FLAG
Banana bread, banana laffy taffy, banana runts candy, banana coffee syrup
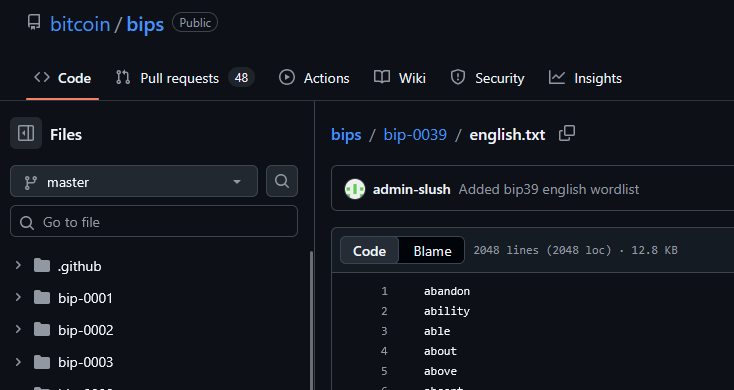
Managing my plants (75 Points)
Find the seed phrase that was copied and saved.
There are a few seed phrases you can find in ALEAPP, but as you only get one chance for this challenge, you need to find the one that was actually saved. Here’s the easiest way to do this:
First, we want to make sure that we have captured a list of all the potential seed phrases in the RAM image. To do this, first download the Bitcoin BIP-39 wordlist for seed phrases. It is 2048 words long.
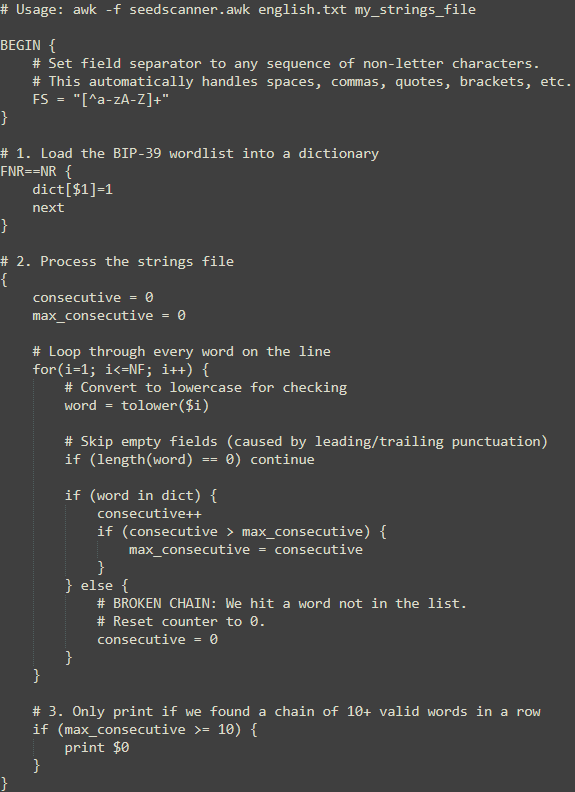
Create an awk script to take this and your strings file to filter for potential seed phrases.
Now run this against the strings file, and direct output to a separate, new file.
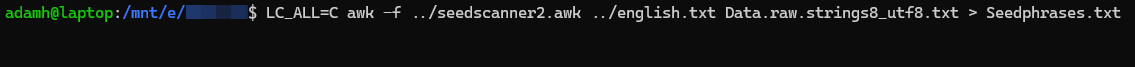
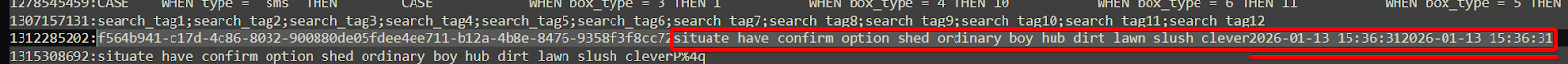
We can confirm from this smaller file, that we are left with 3 possible seed phrases:
1. situate have confirm option shed ordinary boy hub dirt lawn slush clever
2. story drop control sad motor finish region chicken clump exercise camera before
3. artefact dismiss paper sick bright exhibit obey ghost offer almost swallow clap
However, we can see that one of the seed phrases has a timestamp attached.
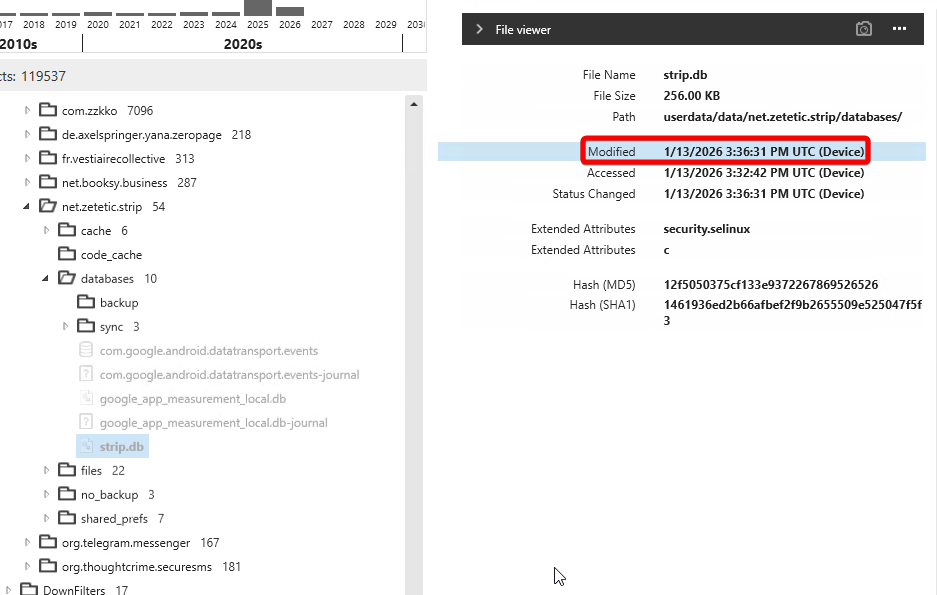
Looking at the question again, if the seed phrase was saved, it was likely saved to the password manager. If we investigate the DB for the Codebook Password Manager app, we can see that the strip.db is encrypted, but was last modified at the exact time that is associated with the seed phrase.
FLAG
situate have confirm option shed ordinary boy hub dirt lawn slush clever